By Sam Abuelsamid, Senior Research Analyst – Navigant Research
If you move, you will die. If you don’t move, you are already dead. There are countless variations on that theme but the gist is that life is full of risk and, sooner or later, it will get you. However, if you plan ahead and prepare, you can minimize risk and mitigate its impacts. When it comes to electronic systems, especially in the automotive environment, it’s time to drop cyber-security and start talking about cyber-resilience.
If you want a car that’s absolutely secure against cyber-attacks, you’ll have to drive something built before about 1970. For the rest of us, living with ever-increasing digital control of our rides, we’re just going to have to take all reasonable measures to keep the bad actors at bay. Make no mistake, there are people actively trying to pick the locks on the transportation ecosystem.
While cyber-attacks have become all too common in recent years, the good news (if there is any) is that an estimated 90 percent or more are committed for financial reasons. Hackers are tapping into systems to steal money or data that will eventually translate into money. The same scenario is likely to hold true as these attackers move into the transportation arena. While this sort of attack can be expensive and time-consuming to rectify, it doesn’t typically end in death and destruction.
This is why an attack against Target or Sony Pictures differs from an attack against OnStar or UConnect. In the past year, security researchers have publicly demonstrated the ability to remotely take over vehicles with telematics systems and manipulate acceleration, braking, steering, and other systems. If executed on a broad scale, such an attack could cause mass casualties. Unfortunately, that means anyone hoping to take advantage of electric propulsion faces some degree of risk. That’s because pretty much all of the plug-in electric vehicles (PEVs) currently offered include built-in telematics systems that enable owners to remotely manage charging and precondition the climate control. On the plus side, PEVs are at no more inherent risk than any gas or diesel burner with a telematics system.

Fortunately, there is no evidence at this point that such an attack has ever occurred in the wild, or even that it could be perpetrated on a mass scale. The researchers involved in both demonstrations acknowledge that determining how to remotely connect to the vehicles in question took many months of work, as well as physical access to the vehicle in advance.
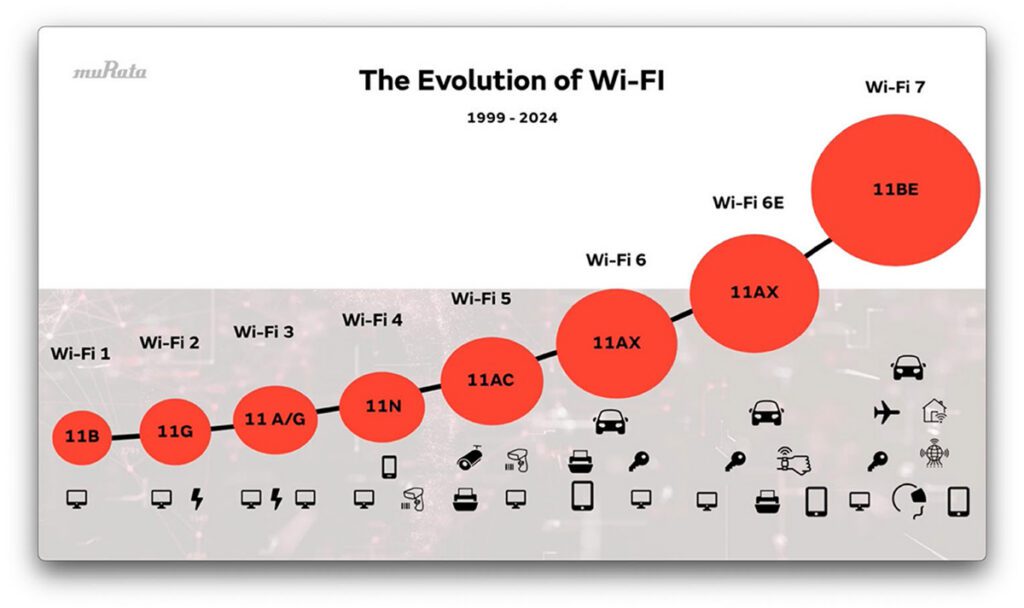
The transportation industry has finally woken up to the reality of the threat, and is moving aggressively to make systems more resilient at all levels. In the next decade, we’ll see a significant ramp-up in the adoption of both connected and automated vehicle systems on PEVs and fuel burners. Cars will get connected through WiFi-based vehicle-to-external communications and cellular-based telematics. OEM telematics systems such Hyundai’s BlueLink and GM’s OnStar will come from the factory, while aftermarket systems like Verizon’s Hum connect to the vehicle via the OBD-II port. The behavior monitoring modules provided by insurance companies in exchange for premium discounts also connect via the diagnostics port and provide a potential entry point for hackers.
In the wake of the public demonstrations in 2015, many pundits called for air-gapping the communications systems in vehicles to prevent a remote takeover. While such an approach would make a system more resistant to attack, it wouldn’t guarantee safety. The physical proximity of systems in a vehicle means an attack that utilizes electromagnetic interference can’t be completely ruled out.
Disconnecting the communications systems from vehicle control systems would also negate the many potential benefits of connected vehicles. In addition to charging management in PEVs, fully or semi-autonomous vehicles can be self-parked or summoned when they are connected.
Rather than disconnecting, OEMs and suppliers are reexamining the entire electronic architecture of new vehicles from cradle to grave. Current vehicles have from 50 to 75 discrete electronic control units managing every aspect of the vehicle, each with the potential for exploits. One approach being promoted by chip-maker Intel is to switch to an integrated controller using a single more powerful processor and the same sort of virtualization technology used on network servers. This approach is claimed to provide improved performance and security by sandboxing all of the different processes.
Regardless of whether a vehicle has one or 100 electronic control units (ECUs), they all need software, and new tools and processes are being developed to test and validate the code. With as much as 100 million lines of source code in new vehicles, this is particularly important, especially in the wake of the Volkswagen diesel emissions scandal. The VW cheating system was executed entirely in software, which is extremely difficult to examine.
No matter how rigorous the testing, it’s virtually impossible to guarantee completely bug-free software, especially in something as complex as an automobile. Thus, numerous companies have popped up in recent years to develop intrusion detection systems that sit on the network to monitor data traffic for anything that looks nefarious. These include both dedicated hardware modules and software detectors that are embedded in one of the existing ECUs.
Most of the major automakers have also come together to launch an information sharing and analysis center that will compile vulnerability information from multiple sources and share that, along with mitigation recommendations, with member companies. Several automakers, including Tesla and GM, have also launched responsible disclosure programs through which security researchers can submit security vulnerabilities that they have discovered, so that they can be corrected by the automakers before being made public.
Finally, incumbent automakers are preparing to follow Tesla down the path of delivering over-the-air software updates for their vehicles. Until Tesla launched Model S in 2012, software updates had to be installed by dealer service technicians. However, considering the reality that increasingly sophisticated electronic systems will require regular updates, that’s no longer a practical solution, especially for security vulnerabilities that need to be distributed and installed as quickly as possible.
The transportation industry has recognized that absolute cyber-security really isn’t possible, but improved development, monitoring, and remediation can make the future mobility ecosystem much more cyber-resilient.
This article originally appeared in Charged Issue 25 – May/June 2016. Subscribe now.